Digital Prism Start 309-249-9397 Inspiring Caller Verification
Digital Prism Start 309-249-9397 reframes caller verification as a context-aware, risk-sensitive process. It moves beyond static IDs toward adaptive assessments that combine layered checks, dynamic risk scoring, and corroborated data. The approach aims to validate callers within the transaction flow, preserving user autonomy while reducing fraud and leakage. It offers transparent, structured workflows and actionable insights for stakeholders, yet leaves critical decisions to trusted safeguards—prompting a closer look at its practical implementation.
What Is Trusted Caller Verification and Why It Matters
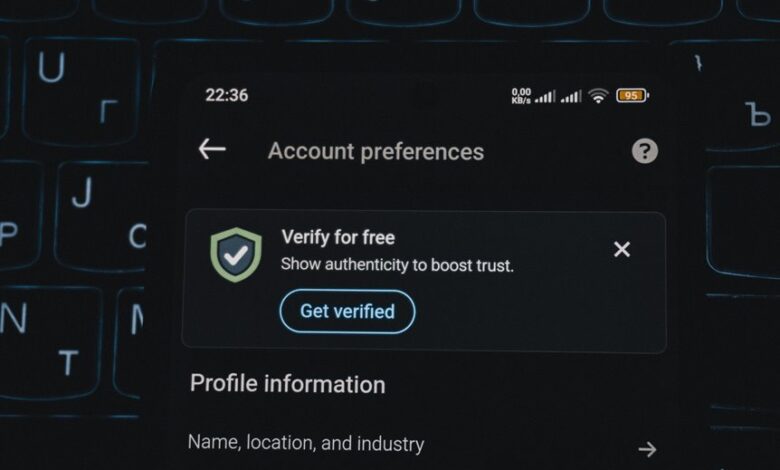
Trusted Caller Verification is a verification framework that confirms a caller’s identity before proceeding with sensitive actions or data access. It enables secure interactions by validating caller identity and ensuring only authorized requests advance. This approach delivers trustworthy verification, reducing fraud and leakage. It supports user autonomy while preserving control, balancing security with freedom, and clarifying risk management for stakeholders.
How Digital Prism 309-249-9397 Reframes Call Authenticity
Digital Prism reframes call authenticity by shifting the focus from mere caller identification to contextual verification, ensuring that each interaction is evaluated within its specific risk and flow.
The approach embodies reframing trust through adaptive assessment, aligning verification with transaction context.
It elevates caller authentication as a dynamic, strategic safeguard, empowering users with intentional autonomy and transparent protection.
Practical Verification Techniques You Can Use Today
Practical verification techniques available today emphasize contextual checks over superficial identifiers, enabling organizations to confirm legitimacy efficiently. Identification techniques focus on corroborated data, while robust Caller identity assessment reduces reliance on static badges. Verification challenges are addressed through layered trust metrics, dynamic risk scoring, and continuous monitoring. This approach preserves authenticity, supports autonomy, and sustains secure communications without constraining freedom.
Real-World Scenarios: From Suspicion to Confident Calls
In real-world calls, teams move from initial suspicion to confident verification by applying layered checks that blend contextual insight with real-time risk signals.
This process emphasizes suspicion resolution through structured workflows, adaptive questioning, and corroborating data.
As patterns emerge, confidence building becomes measurable, enabling informed judgments and decisive action while preserving user autonomy and trust in the verification framework.
Conclusion
In essence, trusted caller verification offers a polite, reliable path through uncertainty. Digital Prism reframes authenticity as a layered, risk-aware process, blending corroborated signals with adaptive scoring to reduce leakage and misreads. Practitioners gain a transparent, flexible framework that honors user autonomy while strengthening safeguards. For sensitive exchanges, this approach nudges interactions toward confidence, clarity, and smoother outcomes, subtly guiding decisions without imposing rigidity. A prudent balance, it quietly elevates trust across the entire transaction flow.




